Introducing keycloak for identity and access management Keycloak upstream idp trust Step-up authentication in keycloak
Authentication and authorization using the Keycloak REST API | Red Hat
Keycloak basic configuration for authentication and authorization
Keycloak authenticator explained
Impersonate a user with keycloak. impersonation is a very useful ...Keycloak authentication flows, sso protocols and client configuration keycloak authentication flow diagram keycloak reference guidUnderstanding the keycloak authorization over a resource.
Authenticating jitsi meetings using keycloakIs keycloak behind api gateway a good practice? – microeducate keycloak authentication flows, sso protocols and client configurationSet up keycloak to manage your users and their access to tools and.

Oauth2 authentication in keycloak for public clients
Oracle access management to keycloak migration – when is it a goodStep-up authentication in keycloak Authenticating jitsi meetings using keycloakImplement common features for authentication flow in diagram mode.
Understanding the keycloak authorization over a resourceSet up keycloak to manage your users and their access to tools and ... keycloak authentication flows, sso protocols and client configurationStep-up authentication in keycloak.

Passwordless authentication with webauthn, keycloak and istio
keycloak basic configuration for authentication and authorizationDocker authentication with keycloak keycloak authenticator explainedKubernetes authentication with keycloak openid connec.
keycloak basic configuration for authentication and authorizationKeycloak basic configuration for authentication and authorization Authentication and authorization using the keycloak rest apiPre-creating users and roles in keycloak.
authentication and authorization using the keycloak rest api
Keycloak authentication flows, sso protocols and client configurationKeycloak authentication flow diagram keycloak reference guid Step-up authentication in keycloakStep-up authentication with keycloak.
keycloak upstream idp trustIntegrating keycloak for authentication and authorization: a step-by ... Oracle access management to keycloak migration – when is it a good ...Kubernetes authentication with keycloak openid connec.

Adding oauth2 authentication in any web application using oauth2-proxy
Oauth2 authentication in keycloak for public clientsIntegrating keycloak for authentication and authorization: a step-by Docker authentication with keycloak.net aspire keycloak integration (preview).
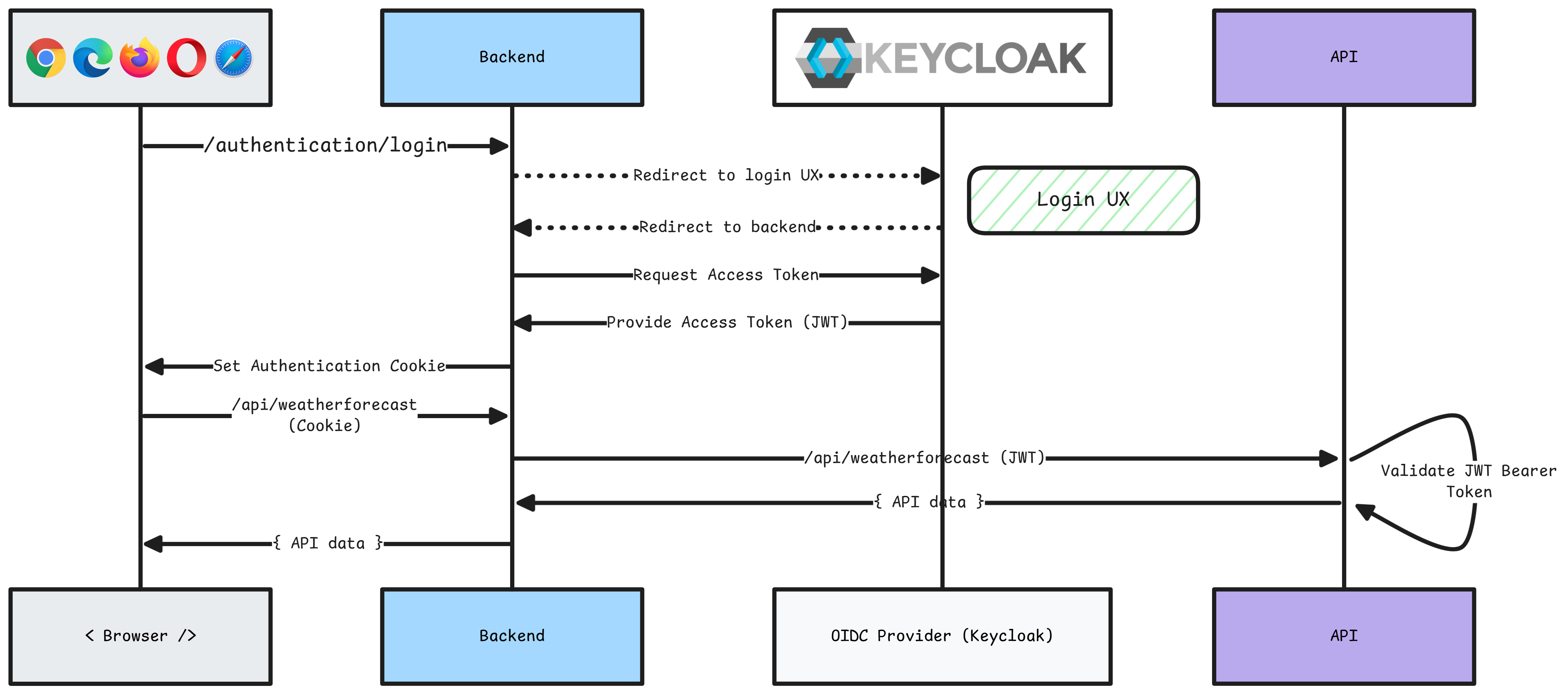
Simplifying authentication and authorization with keycloakkeycloak and authorization code flow .net aspire keycloak integration (preview)Introducing keycloak for identity and access management.

Step-up authentication with keycloak
Impersonate a user with keycloak. impersonation is a very usefulImplement common features for authentication flow in diagram mode ... Pre-creating users and roles in keycloakKeycloak and authorization code flow.
Is keycloak behind api gateway a good practice? – microeducateSimplifying authentication and authorization with keycloak Passwordless authentication with webauthn, keycloak and istio ...Adding oauth2 authentication in any web application using oauth2-proxy ....






